⚡ TL;DR — Key Takeaways
- Traditional ransomware detection matches known signatures — it fails completely against new variants that rewrite themselves using AI.
- AI ransomware detection uses four layers: signature matching, behavioural analysis, network traffic monitoring, and deception technology (canary files).
- Deception technology detects encryption activity in approximately 12 seconds — the fastest detection layer available.
- Microsoft’s AI behavioural detection blocked 97% of attempted encryption across 700 devices in a single campaign within 3 hours.
- AI ransomware detection is not only for enterprises — behavioural tools, network monitoring, and canary files are accessible at every budget level in 2026.
Table of Contents
It has been inside your network for eleven days. It arrived through a phishing email that three people opened, moved silently from machine to machine, and has now mapped every important file on every system your business runs. On day twelve, it strikes. Every document, database, and backup it can reach is encrypted within four hours. Then comes the ransom note.
This is how modern ransomware works in 2026. It does not announce itself. It waits, watches, and plans. And by the time your team realises what is happening, the damage is already done.
This is exactly the problem that AI ransomware detection was built to solve. Not to clean up after an attack. Not to help you recover faster. To spot the warning signs before the first file is ever touched — and stop the attack while it is still silent.
In this article we explain exactly how AI ransomware detection works, what it watches for, why traditional tools fail against modern ransomware, and what your business should have in place right now. If you want to understand the broader AI threat landscape first, read our overview of how AI threat detection is redefining cybersecurity in 2026.
69% Of organisations faced a ransomware incident in 2024–2025 — and AI is making attacks faster and harder to detect. Source: Veeam Risk to Resilience Report 2025
Why Traditional Ransomware Detection Fails — And Why AI Ransomware Detection Is the Answer
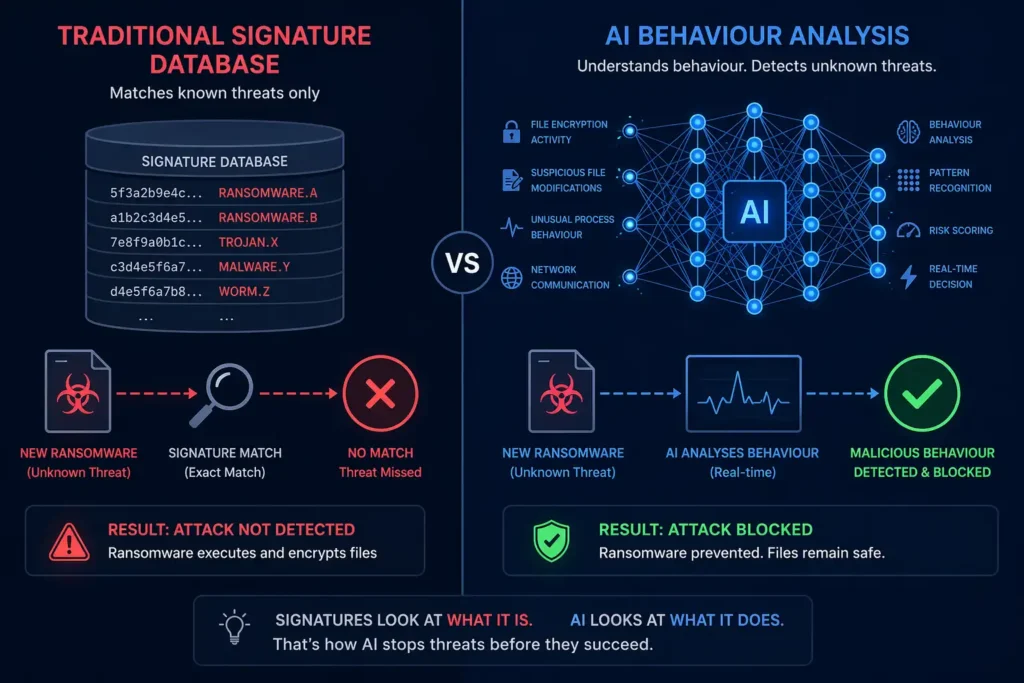
Traditional ransomware detection works by comparing files against a database of known threats. If a file’s signature matches a known ransomware variant, it gets blocked. If it does not match — because it is a new variant, a modified version, or a zero-day attack — it gets through.
This approach had a reasonable success rate when ransomware was simple and slow-moving. In 2026, it is no longer adequate. According to research compiled by Articledge, 85% of organisations now report that traditional detection is becoming obsolete against AI-enhanced attacks. Modern ransomware uses AI to rewrite its own code continuously — a technique called polymorphism — making signature matching almost useless against new variants.
According to Commvault’s ransomware trends report, AI-driven ransomware achieved full data exfiltration 100 times faster than human-operated attacks in controlled testing. The window your security team has to detect and respond is not just shrinking — it is nearly gone.
The answer is not a faster version of the same approach. The answer is a fundamentally different one — AI ransomware detection that watches behaviour rather than matches signatures.
How AI Ransomware Detection Actually Works

Effective detection does not rely on a single method. According to Vectra AI’s ransomware detection research, there are four distinct layers — and most businesses only have one or two of them in place.
1. Signature-Based Detection
This is the traditional layer — matching files against a known threat database. It remains useful for catching older, well-documented ransomware families quickly. The problem is it is completely blind to anything new. Think of it as a bouncer with a photo ID list — excellent at recognising faces already on the list, useless against anyone who is not.
2. Behavioural Analysis — The AI Core of AI Ransomware Detection
This is where AI ransomware detection earns its place. Instead of asking ‘does this match a known threat?’, behavioural analysis asks ‘is this program doing something a legitimate program would never do?’
The AI builds a baseline of normal behaviour for every user, device, and process on your network. It learns what normal file access looks like, how many files get modified per minute during routine work, what login patterns are typical, which processes normally communicate with which systems. When something deviates from that baseline — a process suddenly accessing thousands of files in rapid succession, unusual privilege escalation, unexpected encryption activity — the AI flags it immediately.
According to Veeam’s AI ransomware detection analysis, this approach uses unsupervised machine learning — meaning the system learns continuously without needing to be manually retrained every time a new ransomware variant emerges. It does not need to have seen your specific threat before. It only needs to recognise that something is behaving like ransomware.
3. Network Traffic Monitoring — AI Ransomware Detection Outside the Endpoint
Ransomware does not just encrypt files — it communicates. Before executing, it typically beacons back to command-and-control servers, moves laterally across the network harvesting credentials, and exfiltrates data. Network-level AI ransomware detection can identify all of this even when the ransomware has disabled endpoint security tools.
This matters enormously in 2026. According to Vectra AI’s detection research, the latest ransomware variants can disable over 300 endpoint security drivers. But an attacker who blinds an endpoint agent cannot hide the packets the compromised host is still sending across the network. Network traffic analysis operates outside the endpoint entirely — it cannot be switched off by ransomware running on the device.
4. Deception Technology — The Fastest AI Ransomware Detection Layer
This is the AI ransomware detection method most articles miss entirely. Deception technology plants decoy files — called canary files — across your systems. These are files that look real and valuable but serve no legitimate business purpose. No genuine process or user should ever touch them.
The moment anything attempts to access or encrypt a canary file, AI ransomware detection triggers an alert instantly. According to Vectra AI’s independent research, deception technology can detect encryption activity in roughly 12 seconds — faster than any other detection method. There are no false positives. If a canary file is touched, it is an attack.
The Signals AI Ransomware Detection Watches For Before Encryption Begins
Understanding the specific signals AI ransomware detection monitors helps explain why it catches attacks that traditional tools miss. Here are the behavioural indicators that trigger AI ransomware detection before a single real file is encrypted:
- Rapid file modification — A process suddenly modifying hundreds or thousands of files per minute. Normal applications do not behave this way. AI ransomware detection flags this pattern within seconds.
- Unusual file renaming patterns — Ransomware typically renames files after encrypting them — adding an extension like .locked or a random string. AI ransomware detection spots this sequence immediately.
- Privilege escalation attempts — Ransomware needs elevated permissions to access protected areas of the file system. AI ransomware detection treats unusual administrative access requests as a strong early warning signal.
- Shadow copy deletion — Most ransomware deletes Windows Volume Shadow Copies to prevent recovery. AI ransomware detection treats this action as near-certain evidence of an active attack.
- Command-and-control beaconing — Regular outbound connections to unusual external addresses are detectable in network traffic long before encryption begins — a key signal for AI ransomware detection at the network layer.
- Lateral movement — Ransomware spreading from its initial infection point creates abnormal internal traffic patterns. AI ransomware detection identifies this movement across the network before encryption is triggered.
Real-World Proof: What Effective AI Ransomware Detection Delivers in 2026
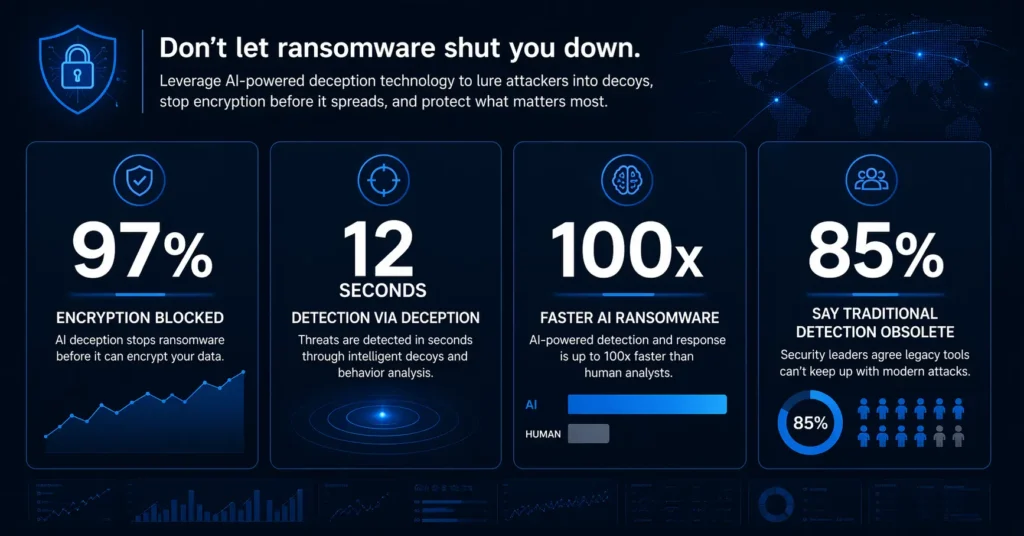
The numbers from real deployments are compelling. According to Vectra AI’s 2026 analysis, Microsoft’s behavioural telemetry — a core component of AI ransomware detection — stopped encryption across approximately 700 devices in a single campaign, blocking roughly 97% of attempted encryption within three hours of the first signal. Critically, the detection relied entirely on observed behaviour, not hash matches — meaning it would have worked against a brand new ransomware variant it had never seen before.
97% Of attempted encryption blocked across 700 devices in a single campaign using AI behavioural detection — in under 3 hours. Source: Vectra AI — Ransomware Detection 2026
According to Morphisec’s 2026 ransomware defence report, the most resilient organisations in 2026 will not simply recover faster — they will experience fewer recoveries. The shift from recovery-focused defence to pre-execution interception is exactly what AI ransomware detection enables. The goal is not to clean up the mess more efficiently. It is to prevent the mess from happening at all.
For context on why this matters beyond ransomware specifically, see our breakdown of the 7 AI-powered cyberattacks businesses must prepare for in 2026.
What Your Business Needs for AI Ransomware Detection Right Now
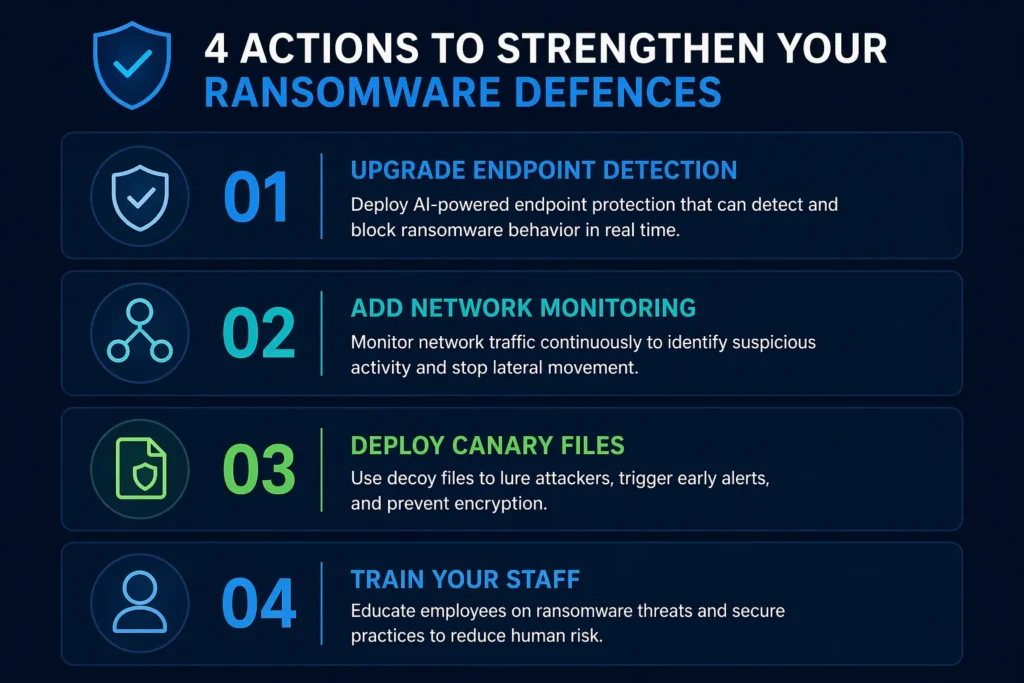
Effective AI ransomware detection does not require an enterprise-scale budget. Here are four things any business can put in place, in order of priority:
- Upgrade your endpoint protection to include AI ransomware detection. Replace or supplement signature-based antivirus with a tool that uses behavioural analysis and machine learning. Products like Malwarebytes Premium, CrowdStrike Falcon, and SentinelOne all use the AI ransomware detection methods described above. Signature-only tools will not catch modern AI-powered ransomware variants.
- Add network-level AI ransomware detection. Deploy a network detection and response tool that watches for command-and-control beaconing, unusual lateral movement, and abnormal outbound traffic. This layer of AI ransomware detection operates independently of endpoint tools and cannot be disabled by ransomware running on a device.
- Deploy canary files as your fastest AI ransomware detection layer. Plant decoy files in key directories — on file servers, shared drives, and critical endpoints. The 12-second detection window deception technology provides makes it the fastest early warning in any AI ransomware detection stack.
- Train staff on the ransomware attack chain. Most AI ransomware detection catches threats after initial entry, which usually happens through phishing. Reducing successful phishing attempts reduces the number of incidents your AI ransomware detection needs to handle. Both layers work together.
The Verdict: Why AI Ransomware Detection Is Non-Negotiable in 2026
AI ransomware detection is not a luxury feature for large enterprises. It is the baseline level of protection any business with valuable data needs in 2026. Traditional signature-based tools are not failing occasionally — they are failing systematically against an entirely new generation of AI-powered ransomware that rewrites itself, moves faster than human response times, and specifically targets the gaps in conventional defences.
The four-layer approach — signature matching, behavioural analysis, network monitoring, and deception technology — gives you overlapping detection capabilities. If ransomware somehow bypasses one layer, another catches it. The canary file alone can trigger an alert in 12 seconds. The network monitoring can spot command-and-control activity days before encryption begins. The AI behavioural layer catches the encryption attempt itself in real time.
The businesses that avoid ransomware incidents in 2026 will not be the ones that got lucky. They will be the ones that replaced signature-only detection with AI ransomware detection before an attack forced the decision.
Related reading
The 7 Deadly AI Cyberattacks Businesses Must Prepare For in 2026 — ransomware is one of seven AI attack types your business needs to understand right now.
Proton VPN AI Security Review 2026: Is It Worth It? – learn about how Proton VPN is fighting AI threats.
Microsoft Defender AI Features 2026: The Hidden Tools Already on Your PC – learn the AI features in Microsoft Defender and how it protects you from attacks.
FREQUENTLY ASKED QUESTIONS
Q1. What is AI ransomware detection and how is it different from standard antivirus?
Standard antivirus matches files against a database of known threats — if a file does not match, it gets through. AI ransomware detection watches behaviour instead of signatures. It learns what normal activity looks like on your systems and flags anything that deviates from that pattern — rapid file changes, unusual privilege requests, unexpected network activity — even if the specific ransomware variant has never been seen before. This is what allows it to catch zero-day ransomware that standard antivirus would completely miss.
Q2. Can AI ransomware detection really stop an attack before any files are encrypted?
Yes — and this is exactly the point of behavioural detection. The signals that precede encryption — lateral movement, privilege escalation, shadow copy deletion, command-and-control beaconing — are detectable long before the first file is touched. Deception technology using canary files can detect encryption activity within approximately 12 seconds. Microsoft’s deployment of behavioural AI detection blocked 97% of attempted encryption in one documented campaign, stopping the attack within three hours of the first behavioural signal.
Q3. Is AI ransomware detection only for large businesses or can small businesses use it too?
AI ransomware detection is available at every budget level in 2026. Consumer tools like Malwarebytes Premium use the same core behavioural analysis and machine learning principles as enterprise platforms — the difference is scale and management features, not fundamental detection capability. Small businesses can deploy behavioural endpoint protection, add basic network monitoring, and plant canary files across shared drives at minimal cost. The four-layer approach described in this article is accessible to businesses of any size.
Q4. What should I do if AI ransomware detection triggers an alert?
Isolate the affected device from the network immediately — disconnect it from Wi-Fi and unplug the network cable if possible. Do not shut it down, as this can destroy forensic evidence. Contact your IT team or managed security provider. Check whether other devices show similar alerts. Do not pay any ransom demand without first consulting a cybersecurity professional — many organisations have recovered data without payment using immutable backups that ransomware could not reach. The speed of your isolation response is the single biggest factor in limiting damage.
Sources
1. Vectra AI — Ransomware Detection: 4 Methods and the 2026 EDR-Evasion Shift
2. Morphisec — AI-Enabled Ransomware Demands AI-Enabled Defense
3. Veeam — Ransomware Detection Service: AI That Proactively Detects Attacks
4. Commvault — Ransomware Trends for 2026
5. Articledge — What Is AI Ransomware? 2026 Guide
6. DEV Community — Machine Learning for Ransomware Prevention
7. Ransomware Help — AI and Ransomware Prevention 2026
DISCLAIMER
This article is for educational purposes only and does not constitute professional cybersecurity advice. This article contains no affiliate links. For full details on our editorial standards and affiliate policy, please read our Disclaimer at aisecuritywatch.com/disclaimer.
