
⚡ TL;DR — Key Takeaways
- Five of the biggest data breaches of 2026 — Stryker, Panera Bread, Navia, Figure Technology, and Match Group — exposed data belonging to tens of millions of people across healthcare, finance, food, and technology sectors.
- None of these data breaches involved technically complex attacks. Most required only a stolen credential, a phishing email, or a social engineering call.
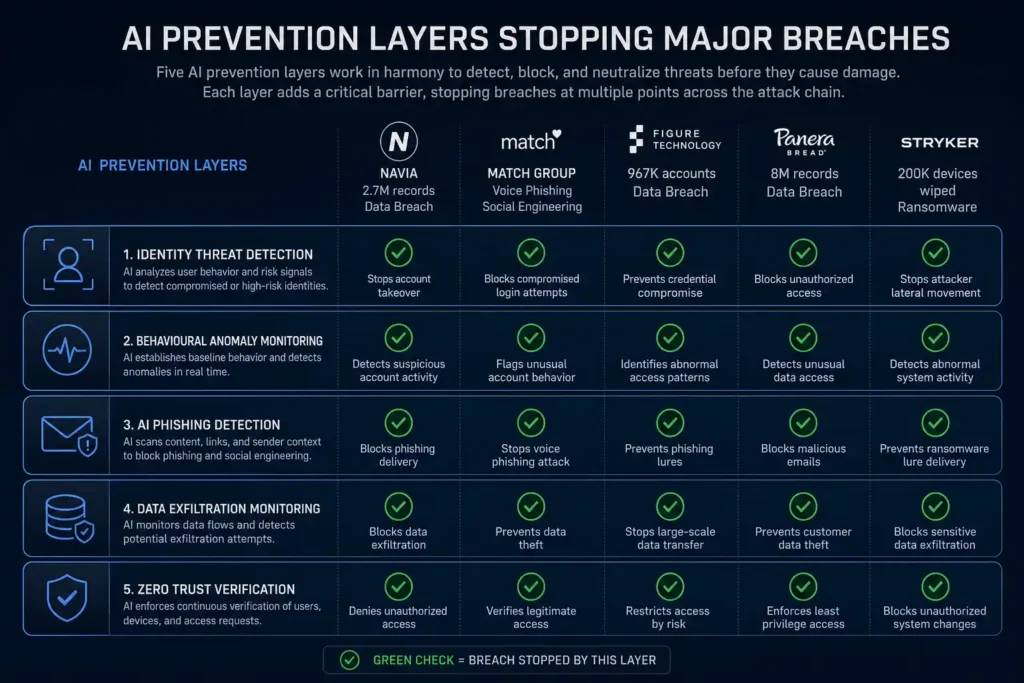
- AI-powered behavioural detection, anomaly monitoring, and identity threat detection could have identified the warning signs in each case before data was exfiltrated.
- The average cost of a data breach in 2026 is $4.4 million — and it takes companies an average of 241 days to detect one.• The pattern across all five incidents is identical: the controls that would have stopped these data breaches were either absent, untested, or ignored.
Table of Contents
Could the biggest data breaches of 2026 have been prevented? In almost every case, yes. According to Strobes’ March 2026 breach analysis, what connects the worst data breaches of 2026 is not attacker sophistication. Most were not technically complex. What connects them is that the controls that would have stopped them were either absent, untested, or ignored.
A single stolen password wiped 200,000 devices at a global medical company. A voice phishing call gave attackers access to a dating platform used by hundreds of millions. A social engineering email handed hackers the keys to a fintech lender’s customer database. These were not inevitable events. They were failures of detection — and in each case, AI-powered tools available in 2026 could have caught the warning signs before the damage was done.
Here are the five most significant data breaches of 2026 so far — what happened, who was affected, and exactly what AI could have prevented in each case. For context on the attack types behind these data breaches, read our guide on the 7 deadly AI cyberattacks businesses must prepare for.
241 days Average time companies take to identify and contain a data breach in 2026. The average breach costs $4.4 million globally — over $10 million in the US.Source: Breachsense — Data Breach Statistics 2026
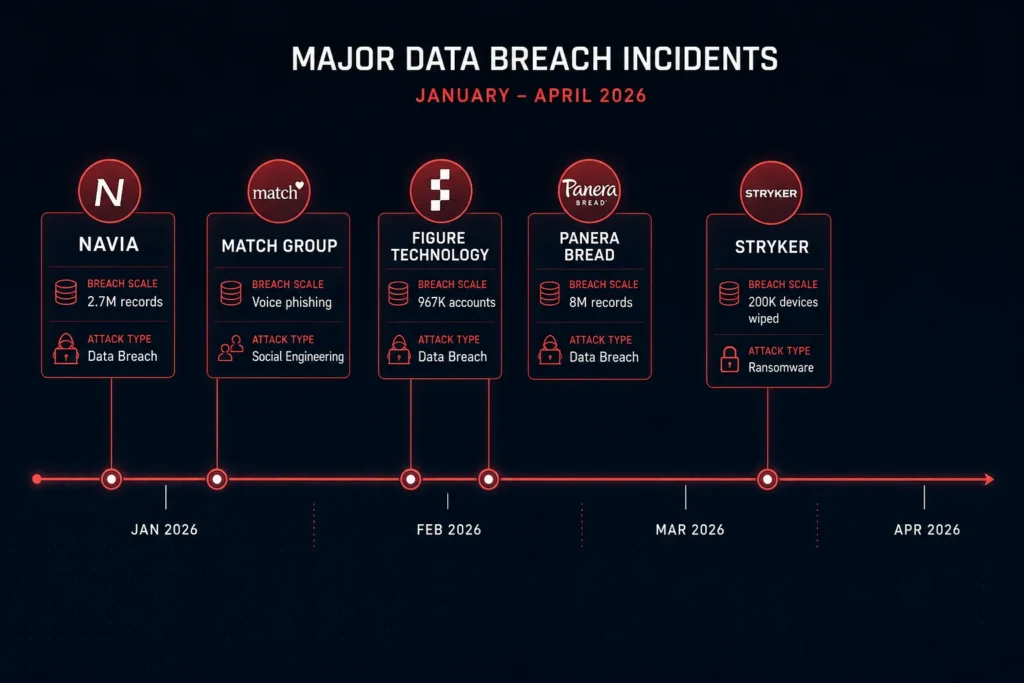
BREACH #1 [ March 2026 ]
Stryker — 200,000 Devices Wiped Across 79 Countries
Scale: 200,000+ devices wiped across 79 countries. 50TB data claimed stolen.
Attack type: Credential compromise + MDM exploitation (no malware deployed)
What AI could have prevented: Identity threat detection on the compromised admin account + anomaly detection on unusual MDM activity
At 5am UTC on 11 March 2026, employees at medical device giant Stryker across 79 countries watched their screens go black. According to Strobes’ detailed breach analysis, Iran-linked group Handala had compromised a single Microsoft Intune administrator account, created a new Global Administrator account, and used Stryker’s own device management platform to remotely wipe over 200,000 devices. No malware. No ransomware. Just a legitimate IT tool turned against the company that owned it.
This data breach stopped manufacturing. Shipping halted. Locations reverted to pen and paper. The FBI seized Handala’s websites on March 19.What AI could have prevented: AI-powered identity threat detection would have flagged the creation of a new Global Administrator account at 5am as anomalous behaviour — a high-risk action no legitimate workflow requires at that hour. Behavioural AI monitoring the MDM platform would have detected the mass device wipe command as unprecedented and blocked it pending verification. This data breach required only one compromised credential. AI anomaly detection on privileged account activity is a documented, available defence.
BREACH #2 [ January–February 2026 ]
Panera Bread — 8 Million Customer Records Exposed
Scale: 8 million+ customer records including names, dates of birth, phone numbers, email addresses.
Attack type: Social engineering — ShinyHunters compromised Microsoft Entra SSO credentials
What AI could have prevented: AI-powered phishing detection + identity provider anomaly monitoring
The American bakery-café chain suffered one of the largest consumer data breaches of 2026. According to Proton’s Data Breach Observatory, the criminal group ShinyHunters gained access to Panera’s internal systems by compromising a Microsoft Entra Single Sign-On credential. The data breach exposed over 8 million customer records — names, dates of birth, phone numbers, and email addresses.
ShinyHunters later leaked a 760MB archive when extortion demands went unmet. The volume of contact data stolen is sufficient to fuel targeted phishing campaigns against millions of customers for years.What AI could have prevented: AI-driven identity threat detection monitoring the Entra SSO login would have flagged the credential use as anomalous — unusual login time, unfamiliar device, or location mismatch are all signals modern AI systems flag in real time. AI-powered data exfiltration monitoring would have detected the mass download of 8 million records as abnormal data movement and triggered an alert before the full dataset left the environment.
BREACH #3 [ December 2025 – January 2026 ]
Navia — 2.7 Million People’s Health and Financial Data Exposed
Scale: 2.7 million people. SSNs, health plan data, dates of birth, phone numbers, email addresses.
Attack type: Unauthorized access — undetected intrusion spanning 24 days
What AI could have prevented: AI-powered intrusion detection + real-time data access anomaly monitoring
Benefits administration company Navia disclosed one of the most damaging data breaches of 2026. According to tech.co’s 2026 breach tracker, the data breach took place between December 22, 2025, and January 15, 2026 — a 24-day window during which an unauthorised actor accessed 2.7 million people’s Social Security numbers, health plan information, dates of birth, and financial account details.
The 24-day dwell time — the gap between initial compromise and detection — is what transformed this from a contained incident into a catastrophic data breach. In that window, every record in the affected system was accessible.What AI could have prevented: AI-powered intrusion detection operating continuously would have identified the unauthorised access pattern within hours — not 24 days. Anomaly detection monitoring access to records containing SSNs and health data would have flagged unusual query volumes as a critical alert. The 241-day average data breach detection time drops dramatically with AI monitoring — a 24-day dwell time is entirely preventable with the right tooling.
BREACH #4 [ February 2026 ]
Figure Technology Solutions — 967,000 Accounts via Social Engineering
Scale: 967,200 accounts. Names, dates of birth, email addresses, phone numbers, physical addresses.
Attack type: Social engineering — employee manipulated into providing system access
What AI could have prevented: AI behavioural authentication + employee access anomaly detection
Blockchain-centric fintech lender Figure Technology confirmed a data breach after ShinyHunters manipulated an employee into providing access to internal systems. According to Bright Defense’s 2026 breach tracker, the social engineering attack resulted in the download of files containing data from nearly 967,000 user accounts — names, dates of birth, email and postal addresses, and phone numbers. ShinyHunters posted roughly 2.5GB of stolen customer records online when extortion failed.
This data breach is a clear example of how human trust — not technical vulnerability — is the primary attack surface in 2026. The attacker needed only a conversation.What AI could have prevented: AI-powered behavioural authentication continuously verifies that user actions match established patterns. An employee suddenly downloading files at unusual hours, accessing data outside their normal scope, or transferring large volumes of records — all are detectable in real time. AI systems can enforce step-up authentication or automatic session suspension when access patterns deviate from baseline. Social engineering exploits trust in people, not systems — AI monitoring the access behaviour after that trust is exploited is the last line of defence against this type of data breach.
BREACH #5 [ January 2026 ]
Match Group (Tinder, Hinge, OkCupid) — Voice Phishing via Identity Provider
Scale: Undisclosed volume. Personal and contact information of Tinder, Hinge, and OkCupid users.
Attack type: Voice phishing (vishing) — ShinyHunters targeted Okta identity provider via phone call
What AI could have prevented: AI vishing detection + identity provider anomaly monitoring
Match Group, parent company of Tinder, Hinge, and OkCupid, confirmed a data breach after ShinyHunters conducted a voice phishing campaign targeting its Okta identity provider. According to Proton’s breach observatory, attackers called employees posing as IT support, convinced them to provide access credentials, and used those credentials to access systems through the Okta SSO layer.
This data breach is a textbook example of AI-powered vishing — using convincing voice-based social engineering to bypass technical defences entirely. No malware, no exploit, no vulnerability. Just a phone call.What AI could have prevented: AI-powered identity threat detection on the Okta layer would have flagged the login as anomalous — new device, unusual location, or access pattern inconsistent with the employee’s baseline. Real-time AI vishing detection tools can now identify synthetic or scripted voice patterns during calls. Zero trust architecture requiring hardware-key verification rather than voice-based credential sharing would have made the vishing attempt ineffective regardless of how convincing it sounded.
The Pattern Connecting Every Data Breach on This List
Look at the five data breaches of 2026 above and a single pattern emerges: none required a sophisticated attack. One stolen password. One manipulated employee. One social engineering phone call. One unmonitored access window lasting 24 days. According to ACI Learning’s 2026 breach analysis, many of the biggest data breaches of 2026 were not unstoppable attacks — they were preventable failures.
The root causes across all five data breach incidents are identical: credential compromise exploited without detection, abnormal access patterns not flagged in real time, and data exfiltration that should have triggered automated alerts but did not. The AI tools that address these failure modes — identity threat detection, behavioural anomaly monitoring, data access controls — are documented, widely available, and in most cases not expensive.
What Your Business Can Do to Avoid the Next Data Breach
• Deploy AI-powered identity threat detection — Every data breach on this list began with a compromised credential. AI identity threat detection monitors login behaviour, flags anomalous access patterns, and enforces step-up authentication when something does not match the user’s baseline. Tools like Microsoft Entra ID Protection and Okta ThreatInsight do this automatically.
• Enable behavioural anomaly monitoring on your data — Navia’s 24-day undetected data breach would have ended in hours with AI monitoring watching for unusual database query volumes and access to sensitive record types. Most cloud platforms include basic anomaly detection — turn it on and set alerts for mass data access events.
• Enforce zero trust for privileged access — The Stryker data breach required only one compromised admin account. Zero trust architecture — where every privileged action requires re-verification regardless of who initiated it — would have blocked the MDM wipe command before it executed.
• Train staff specifically on vishing and social engineering — Three of the five data breaches of 2026 on this list involved an employee being manipulated by phone or social engineering. Technical controls stop technical data breach attempts. Only human training stops social engineering. Run realistic vishing simulations — not generic security awareness modules.
Verdict: What 2026 Data Breaches Tell Us About Where Defence Must Go
The data breaches of 2026 are not a story about attacker sophistication. They are a story about detection gaps. Every data breach on this list had a window — a moment between initial compromise and data exfiltration — where AI-powered monitoring could have intervened. In every case, that window was either unmonitored or too slow to matter.
The average 241-day data breach detection timeline means most organisations are discovering incidents months after they occur. AI changes that timeline from months to minutes — but only if it is deployed, configured, and monitored. The organisations that avoid becoming the next data breach headline will not be the ones with the biggest budgets. They will be the ones that closed the data breach detection gap.
For practical guidance on the AI tools that defend against the attack types behind these data breaches, read our review of Microsoft Defender AI features and our guide to AI ransomware detection.
Related reading: AI Threat Detection: How It’s Redefining Cybersecurity in 2026 — the AI systems that could have stopped every data breach on this list.
Dangerous AI Threat Intelligence: Why Every Business Needs It in 2026 – AI threat intelligence to keep your businesses safe.
FREQUENTLY ASKED QUESTIONS
Q1. What were the biggest data breaches of 2026?
The five most significant data breaches of 2026 so far: Stryker (200,000 devices wiped across 79 countries via a single stolen admin credential), Panera Bread (8 million customer records exposed via a compromised Microsoft Entra SSO credential), Navia (2.7 million people’s Social Security numbers and health data accessed over a 24-day undetected intrusion), Figure Technology Solutions (967,000 accounts exposed after a social engineering attack), and Match Group / Tinder (users affected after a voice phishing attack targeted the company’s Okta identity provider).
Q2. How could AI have prevented these data breaches?
In each of the five data breaches of 2026 covered here, AI-powered detection tools could have identified warning signs before data was exfiltrated. Identity threat detection would have flagged anomalous credential use at Stryker and Match Group. Behavioural anomaly monitoring would have caught unusual data access at Navia. AI exfiltration detection would have stopped the mass download of records at Panera. Employee access anomaly detection would have flagged unusual file download behaviour at Figure Technology. The AI tools that address each failure mode are available today.
Q3. How long does it take to detect a data breach in 2026?
The average time to identify and contain a data breach in 2026 is 241 days — nearly eight months. During this window, attackers have unrestricted access to whatever data they initially compromised. AI-powered monitoring dramatically reduces this detection window — from months to minutes in documented cases. The Navia data breach went undetected for 24 days. With AI anomaly detection actively monitoring access patterns, that window would have closed in hours.
Q4. What is the average cost of a data breach in 2026?
The global average cost of a data breach in 2026 is $4.4 million, according to IBM’s Cost of Data Breach report. In the United States, the average exceeds $10 million when factoring in regulatory fines, legal costs, customer notification, and reputational damage. For small and medium businesses, the consequences are often existential — 60% of SMBs that suffer a significant cyberattack go out of business within six months. The cost of AI-powered data breach prevention tools is a fraction of the average breach cost.
SOURCES
1. Strobes — Worst Data Breaches of March 2026
2. Proton — Data Breach Observatory 2026
3. Bright Defense — Recent Data Breaches in 2026
4. tech.co — Data Breaches That Have Happened in 2026
5. PKWARE — 2026 Data Breaches Monthly Tracker
6. ACI Learning — Biggest Cybersecurity Breaches of 2026
7. Breachsense — Data Breach Statistics 2026
8. SharkStriker — April 2026 Data Breaches
9. aisecuritywatch.com — The 7 Deadly AI Cyberattacks 2026
10. aisecuritywatch.com — AI Ransomware Detection 2026
DISCLAIMER
This article is for educational and informational purposes only. All breach details are sourced from publicly disclosed reports and independent security researchers. Breach details may evolve as investigations continue. For full editorial standards, see aisecuritywatch.com/disclaimer.
