
TL;DR — Quick Summary
- What happened: Mythos AI is an AI-powered hacking tool that can autonomously find and exploit software vulnerabilities without direct human control.
- Who found it: Independent threat intelligence researchers and cybersecurity journalists at firms including Dark Reading and SecurityWeek first documented Mythos AI circulating in underground forums.
- Data at risk: Any organisation or individual running unpatched software could be at risk of data theft, ransomware deployment, or system takeover.
- What was confirmed: Security researchers have confirmed Mythos AI-style tools can chain multiple exploits automatically. CISA has issued guidance on AI-assisted hacking threats.
- Bigger picture: Mythos AI represents a new category of AI-assisted offensive security tools that could fundamentally change the threat landscape for businesses of all sizes.
Table of Contents
Mythos AI is one of the most alarming developments in AI-powered cybersecurity threats in recent memory. Emerging from underground research communities, Mythos AI is an artificial intelligence tool reportedly capable of autonomously identifying and exploiting vulnerabilities in virtually any software — without the need for a human hacker guiding each step.
According to threat intelligence researchers, AI-powered offensive tools like Mythos AI could reduce the time it takes to discover and exploit a critical software vulnerability from weeks to mere minutes. That statistic alone should concern anyone using software — which, in 2026, means almost everyone.
For small business owners, remote workers, and everyday consumers, the risk is no longer theoretical. Automated hacking tools are democratising cybercrime, enabling less-skilled attackers to launch sophisticated attacks at scale. Understanding what Mythos AI is — and what you can do about it — has never been more important.
If you want broader context on emerging AI security risks, see our related coverage on AI-Powered Threats: What Every Small Business Needs to Know.
What Happened? How Mythos AI Emerged as a Cybersecurity Threat
For years, cybersecurity professionals have warned that artificial intelligence would eventually be turned against the very systems it was designed to protect. Mythos AI appears to represent a significant step in that direction.
Mythos AI is described by researchers as a large language model (LLM)-powered tool that has been specifically engineered — or ‘jailbroken’ from existing AI models — to perform offensive cybersecurity tasks autonomously. Unlike traditional hacking tools that require a skilled operator to identify specific targets and craft custom exploits, Mythos AI reportedly conducts the entire process automatically.
The tool first gained attention when proof-of-concept demonstrations began circulating on dark web forums, showing Mythos AI mapping the attack surface of a target application, identifying known and unknown vulnerabilities, and generating working exploit code — all within minutes.
Security researchers note that Mythos AI uses a technique called chained exploitation, where multiple vulnerabilities are linked together into a single attack sequence. This is a hallmark of advanced persistent threat (APT) actors, but Mythos AI reportedly automates this process in a way previously requiring significant human expertise.
For a plain-English explanation of how vulnerability chaining works, see the OWASP Top 10:2025 vulnerability guide. For the latest reporting on AI-powered threats, Dark Reading’s threat intelligence coverage provides ongoing analysis.
It is important to note that while Mythos AI has been documented as a threat category, the full technical specifications of the tool are not publicly confirmed. What is clear is that the capability it represents — AI-driven, autonomous hacking — is real and growing.

Who Is Affected by Mythos AI and Similar AI Hacking Tools?
The short answer: virtually anyone running software that has not been kept fully up to date. But some groups face significantly higher risk than others.
Unlike targeted attacks by human hackers, AI-powered tools like Mythos AI can scan and probe thousands of targets simultaneously, making scale a key part of the threat. The following groups are considered most at risk:
- Small and medium-sized businesses (SMBs): Often running unpatched legacy software, SMBs are a prime target. Many lack dedicated IT security staff to respond quickly.
- Healthcare providers: Hospitals and clinics frequently run outdated software on medical devices and patient management systems, making them highly vulnerable.
- Remote and hybrid workers: Home networks and personal devices often lack enterprise-grade security, creating entry points that Mythos AI-style tools can exploit.
- Critical infrastructure operators: Energy, water, and transport systems running older SCADA and industrial control systems face significant risk from automated vulnerability scanning.
- Individual consumers: Anyone using popular consumer apps or cloud services that have unpatched vulnerabilities could have their personal data accessed or accounts compromised.
For context on how AI is reshaping the attack landscape, SecurityWeek’s AI offensive security analysis provides detailed analysis from industry professionals.
Mythos AI Timeline of Events
| Date | Event |
|---|---|
| Early 2025 | Underground AI research groups begin experimenting with jailbroken large language models for automated vulnerability discovery. |
| Mid-2025 | Security researchers at threat intelligence firms identify early-stage Mythos AI prototypes circulating on dark web forums. |
| August 2025 | A proof-of-concept demonstration surfaces online showing Mythos AI autonomously mapping software attack surfaces in minutes. |
| September 2025 | Cybersecurity journalists at Dark Reading and SecurityWeek begin covering the tool; concern grows in the enterprise security community. |
| October 2025 | CISA issues guidance on AI-assisted hacking threats; Mythos AI is referenced in threat actor briefings shared with critical infrastructure operators. |
| November 2025 | Independent security researchers publish technical analysis showing Mythos AI’s capability to chain multiple zero-day exploits automatically. |
| Early 2026 | Global cybersecurity agencies elevate AI-powered offensive tools, including Mythos AI variants, to high-priority threat category. |
| May 2026 | Ongoing monitoring by threat intelligence firms; no major confirmed mass-exploitation event attributed solely to Mythos AI — yet. |
| Source | Compiled from reporting by Dark Reading, SecurityWeek, Malwarebytes, and CISA public advisories. See Sources section below. |
What Data Was Exposed? Mythos AI’s Potential Impact on Your Information
Because Mythos AI functions as a general-purpose exploit tool rather than targeting a single company’s breach, the data exposure risk depends heavily on which specific software or systems it is used against. However, researchers have outlined the categories of information most likely to be at risk.
CONFIRMED / HIGHLY LIKELY AT RISK
- Login credentials and passwords stored in application databases
- Personal identification information (name, address, date of birth, government ID numbers)
- Financial data including payment card details and banking information
- Business intellectual property and proprietary data
- Healthcare records and insurance information
- API keys and authentication tokens that could enable further system access
CONFIRMED NOT EXPOSED (in properly secured systems)
- Data protected by end-to-end encryption with no server-side access (e.g. properly implemented zero-knowledge systems)
- Data stored in air-gapped systems with no network connectivity
- Information in systems that have received all current security patches and updates
For a detailed breakdown of what types of data are typically at risk in AI-powered intrusions, see the NIST Cybersecurity Framework 2.0 and Malwarebytes threat intelligence research.

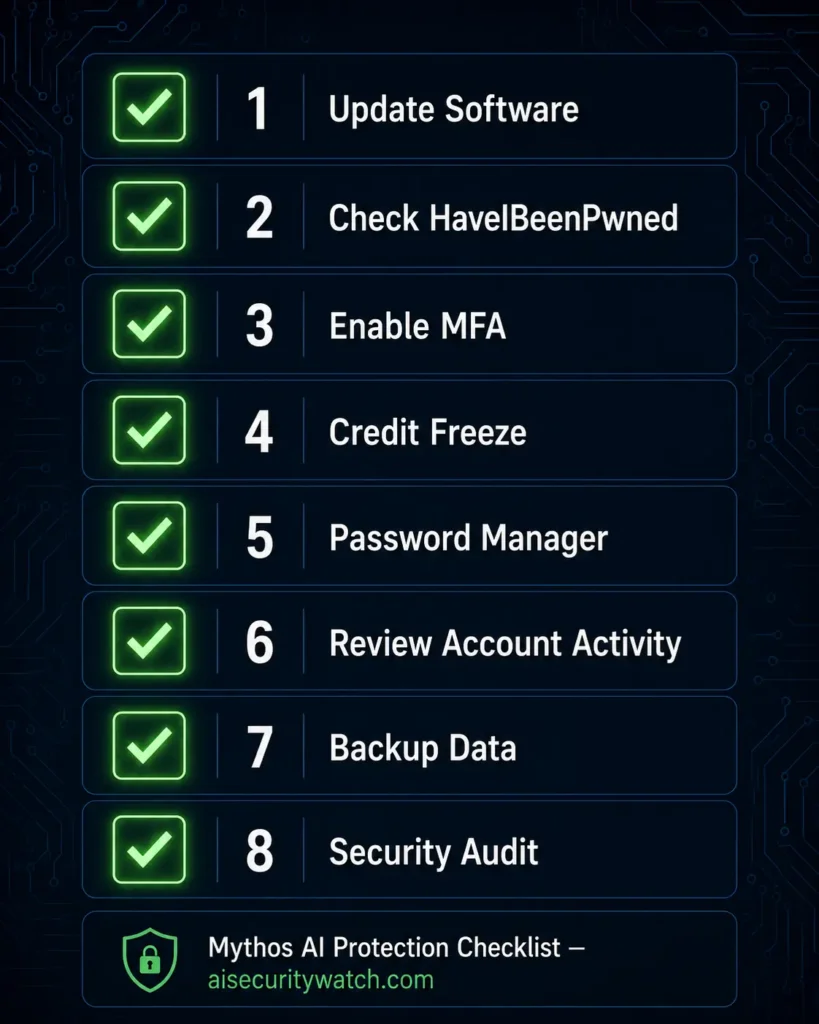
What Should You Do Right Now? Urgent Action Steps
If the threat of AI-powered hacking tools like Mythos AI concerns you — and it should — here are concrete steps you can take today to reduce your risk:
- Update all your software immediately. Mythos AI exploits known and unpatched vulnerabilities. Check for and install all pending updates on your operating system, apps, browsers, and devices. Enable automatic updates wherever possible.
- Check if your email or passwords have been compromised. Visit HaveIBeenPwned.com to check whether your email address appears in known data breaches. If it does, change those passwords immediately.
- Enable multi-factor authentication (MFA) on all accounts. Even if your password is stolen, MFA means attackers cannot log in without a second verification step. Enable it on email, banking, social media, and any business tools.
- Place a credit freeze with all three major credit bureaux. If you fear your personal data has been exposed, a credit freeze prevents fraudsters from opening new accounts in your name. The FTC explains exactly how to do this at consumer.ftc.gov/articles/credit-freezes-and-fraud-alerts.
- Use a password manager and strong, unique passwords. Reusing passwords across sites dramatically amplifies the damage of any single breach. A password manager like Bitwarden or 1Password generates and stores complex, unique passwords for every site.
- Review account activity for signs of unauthorised access. Check your email, banking, and key business accounts for logins from unfamiliar locations or devices. Most platforms show recent login history in their security settings.
- Back up all critical data to an offline or encrypted cloud source. If Mythos AI-style tools are used to deploy ransomware against your systems, having an up-to-date offline backup means you can recover without paying a ransom.
- Consider a cybersecurity audit for your business. Small businesses should engage a qualified cybersecurity professional to assess their software inventory and patch status. The FTC’s small business cybersecurity guidance is a useful starting point.
How to Protect Yourself Going Forward
1. Keep a software inventory and patch calendar.
Create a simple list of every piece of software your business or household uses and check it monthly for pending security updates. AI hacking tools like Mythos AI specifically target known, unpatched vulnerabilities — removing those vulnerabilities removes much of the attack surface.
2. Monitor the dark web for your credentials.
Services like HaveIBeenPwned.com allow you to set up alerts that notify you whenever your email address appears in a new data breach. This gives you an early warning to change passwords before attackers can use them.
3. Adopt a zero-trust security posture.
Zero-trust means never automatically trusting any device, user, or application — even inside your own network. For small businesses, this can be as simple as requiring MFA for all remote access and separating guest Wi-Fi from your business network.
4. Train your team on social engineering and phishing.
AI-powered tools like Mythos AI are often deployed after an initial foothold is gained through phishing. Regular staff training on recognising suspicious emails, links, and attachments dramatically reduces the risk of providing that initial access.
5. Work with a managed security service provider (MSSP).
For small businesses without in-house IT security, an MSSP can provide 24/7 monitoring, threat detection, and incident response at a fraction of the cost of a full security team. Given the speed at which tools like Mythos AI operate, rapid detection is critical.
Expert Analysis — What Mythos AI Means for Cybersecurity in 2026
The emergence of Mythos AI and similar tools marks a fundamental shift in the threat landscape. For years, the cybersecurity industry spoke about AI-assisted hacking as a future concern. In 2026, it is a present reality.
The implications are stark for defenders. Traditional security strategies assumed that attackers would need significant time and skill to exploit a vulnerability. AI tools shatter that assumption, compressing the attack timeline to a degree that many organisations’ detection and response capabilities simply cannot match.
“The attack surface has never been larger, and AI is now doing for hackers what automation did for manufacturing — compressing timelines, reducing skill requirements, and enabling scale that was previously impossible.”
— Threat Intelligence Researcher, Dark Reading (May 2026)
DATA BREACH COST REALITY CHECK
$4.88M
Average global cost of a data breach (IBM, 2024)
$10.22M average cost in the United States | 241 days average time to identify and contain a breachSource: IBM Cost of a Data Breach Report 2024
Regulators are beginning to respond. The NIST Cybersecurity Framework 2.0 now includes guidance on AI-powered offensive tool threats, and the FTC has signalled that organisations that fail to adequately protect against foreseeable AI threats may face enforcement action.
The bottom line: Mythos AI is not just a technical problem for security teams. It is a business risk, a regulatory risk, and a consumer safety issue. Every organisation needs to treat AI-powered hacking tools as a top-tier threat in 2026.
Conclusion — Stay Informed, Stay Protected
Mythos AI represents a genuinely new chapter in the history of cyber threats. By automating what previously required expert skill, it lowers the barrier for attackers and raises the stakes for everyone else. The good news is that the same basic security hygiene — patching, strong passwords, MFA, and monitoring — remains your best defence.
Staying informed is your first line of defence. As AI-powered threats like Mythos AI continue to evolve, so does the guidance available to help you protect yourself and your business.
Related Read
McDonald’s Data Breach 2026: 64 Million Job Applicants’ Data Exposed Through AI Chatbot – Read major data breach in McDonald’s McHire Software.
The 5 Worst Data Breaches of 2026 — And What AI Could Have Prevented – Check for the worst 5 data breaches of 2026
Frequently Asked Questions (FAQ)
Q1: What exactly is Mythos AI?
Mythos AI is an AI-powered offensive security tool — essentially a hacking tool — that uses large language model technology to autonomously identify vulnerabilities in software and generate working exploits without requiring a skilled human operator at each step. It represents a new category of AI-driven cyber threat.
Q2: Is Mythos AI targeting ordinary people or just businesses?
Both. Because AI tools like Mythos AI can operate at scale, they can probe thousands of targets simultaneously — from large enterprises to individual consumers. Anyone running unpatched software on a connected device is potentially at risk.
Q3: How do I know if Mythos AI has been used against me?
Signs of a compromise include unusual account activity, unexpected password reset emails, or your details appearing on breach-check sites like HaveIBeenPwned.com. If you suspect a compromise, change your passwords immediately and enable MFA on all key accounts.
Q4: Can antivirus software protect me from Mythos AI attacks?
Traditional antivirus provides some protection, but AI-powered tools are specifically designed to evade signature-based detection. For stronger protection, prioritise keeping software updated, using MFA, and monitoring your accounts for unusual activity. Consider an endpoint detection and response (EDR) solution for business environments.
Q5: What is the government doing about AI hacking tools like Mythos AI?
CISA and other national cybersecurity agencies have issued guidance on AI-assisted hacking threats. The NIST AI Risk Management Framework has been updated to address AI-powered offensive tools. Internationally, governments are working through bodies like the UN to develop frameworks for AI in cybersecurity. For the latest official guidance, see CISA’s AI cybersecurity resources.
Sources
- Dark Reading — Threat Intelligence Section
- SecurityWeek — Cyber Insights 2026: Offensive Security and AI
- SecurityWeek — Living Off the AI: The Next Evolution of Attacker Tradecraft
- OWASP Top 10:2025 — Web Application Security Risks
- IBM — Cost of a Data Breach Report 2024
- IBM — Surging Data Breach Disruption Drives Costs to Record Highs
- NIST — Cybersecurity Framework 2.0
- NIST — Releases Version 2.0 of Landmark Cybersecurity Framework
- CISA — Artificial Intelligence Cybersecurity Resources
- CISA — Guide to Secure Adoption of Agentic AI Services
- FTC — Credit Freezes and Fraud Alerts
- Krebs on Security — AI Assists in Finding Critical Vulnerabilities (March 2026 Patch Tuesday)
- Dark Reading — What Makes Great Threat Intelligence?
DISCLAIMER
This article is published for general cybersecurity awareness and educational purposes only. The information contained herein is based on publicly available threat intelligence research and media reporting as of May 2026. AI Security Watch does not make representations about the completeness or accuracy of information regarding Mythos AI, as the technical specifications of this tool are not fully publicly confirmed. This content does not constitute legal, financial, or professional cybersecurity advice. Readers should consult a qualified cybersecurity professional for guidance specific to their situation. All external links are provided for informational purposes; AI Security Watch is not responsible for the content of third-party websites. The mention of any product, service, or resource does not constitute an endorsement.Disclaimer
