
⚡ TL;DR — Key Takeaways
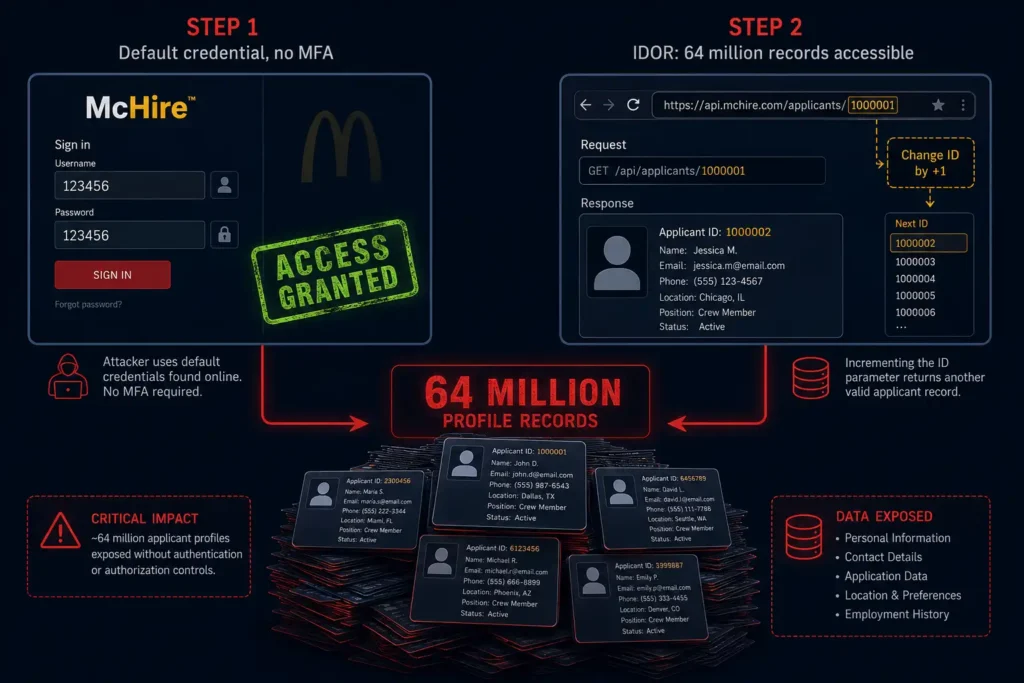
• What happened: Security researchers discovered McDonald’s McHire AI hiring platform had a default admin password of ‘123456’ and an IDOR API flaw, exposing up to 64 million applicant records.
• Who found it: Independent researchers Ian Carroll and Sam Curry, who disclosed it responsibly on June 30, 2025. McDonald’s fixed the credential the same day.
• Data at risk: Names, email addresses, phone numbers, home addresses, chat transcripts, shift preferences, personality test results, and authentication tokens.
• Actual access: Researchers accessed 7 records (5 with personal data) to confirm the flaw. Paradox.ai states no data was leaked or misused by any third party.
• Bigger picture: The flaw exposed a critical industry-wide gap: AI hiring tools deployed at scale without basic security controls like MFA, credential management, or API authorisation.
Table of Contents
In one of the most startling cybersecurity disclosures in recent memory, the McDonald’s data breach involved a hiring platform that exposed the records of up to 64 million job applicants — not through a sophisticated attack, but through a default administrator password of “123456”. The vulnerability was discovered by independent security researchers Ian Carroll and Sam Curry on June 30, 2025, and was reported by SecurityWeek, triggering worldwide attention.
At the heart of the McDonald’s data breach was McHire, the AI-powered recruitment platform used by approximately 90% of McDonald’s 40,000+ global franchisees. McHire features a chatbot called Olivia, built by AI software firm Paradox.ai, which conducts initial job screenings, collects applicant contact details, résumés and shift preferences, and administers personality assessments.
What makes this incident so significant is the sheer scale of records that were at risk, even though the researchers themselves accessed only a small number of records responsibly. As CSO Online reported, the underlying flaw meant anyone with a McHire account could have accessed any of the 64 million applicant records in the system. The McDonald’s data breach is now a reference case for how quickly an AI hiring tool can become a liability when basic security hygiene is skipped.
What Caused the McDonald’s Data Breach? The McHire AI Chatbot Explained
According to TechCrunch’s reporting and the researchers’ own blog post, Ian Carroll and Sam Curry were investigating McDonald’s McHire platform after Reddit users complained about the chatbot’s nonsensical answers. During a routine security review, they noticed a small login link labelled “Paradox team members” on the McHire site. On impulse, they tried the username “123456” with the password “123456”. It worked instantly — granting full administrator access to a live test restaurant account with no multi-factor authentication.
Once inside, the researchers discovered a second, more serious vulnerability. As SecurityWeek detailed, the platform’s internal API had an Insecure Direct Object Reference (IDOR) flaw. By simply changing the applicant ID number in a URL parameter, they could pull the full record of any applicant in the system — including name, address, phone number, email address, chat transcripts, and even an authentication token that could be used to log into McHire as that applicant.
As Adversa AI’s technical breakdown explains, the highest applicant ID the researchers found was 64,185,742 — suggesting the system had processed over 64 million applications. The researchers accessed only 7 records in total to confirm the flaw, then immediately disclosed it responsibly.
For a technical explanation of how IDOR vulnerabilities work, see the OWASP IDOR definition and the OWASP IDOR Prevention Cheat Sheet. This class of vulnerability has ranked #1 in the OWASP Top 10 (under Broken Access Control) since 2021.
McDonald’s attributed the flaw to Paradox.ai and told Wired: “We’re disappointed by this unacceptable vulnerability from a third-party provider.” Paradox.ai’s Chief Legal Officer, Stephanie King, responded: “We take responsibility for this issue. Full stop.” The compromised test account had not been logged into since 2019 and should have been decommissioned, according to Dark Reading’s coverage.
Who Is Affected by the McDonald’s Data Breach?
According to Adversa AI’s analysis, approximately 90% of McDonald’s 40,000+ global franchisees use the McHire platform. This means the applicant pool at risk spans multiple continents and years of hiring activity. While the vulnerability has been patched, the period of exposure — and the scale of records in the system — is significant. The McDonald’s data breach primarily concerns applicants in markets where McHire was actively deployed.
The following groups should take this seriously:
- Anyone who applied for a McDonald’s job through the McHire platform or the McDonald’s careers site, particularly from 2019 onwards
- Current and former McDonald’s employees who were recruited through the McHire system
- Applicants who were never hired — their data was retained in the system regardless
- Young and first-time job seekers — a disproportionately large share of McDonald’s applicants, who may be less equipped to recognise phishing or identity theft
- Applicants in any country where McHire was used, given the platform’s global deployment across franchisees
Paradox.ai has confirmed that only 5 applicants had their data actually viewed by the researchers, and states there is no evidence that any malicious actor accessed the system. As Hackread reported, the vulnerability was fully resolved by July 1, 2025. However, the potential scale of access — 64 million records — makes this one of the most significant AI hiring platform security incidents on record, even where confirmed data exfiltration was limited.
McDonald’s Data Breach Timeline: How It Was Discovered and Fixed
| Date | Event |
| 2019 onward | McHire platform deployed across McDonald’s global franchisee network; test admin account (username/password: ‘123456’) left active and undecommissioned |
| June 30, 2025(afternoon) | Researchers Ian Carroll & Sam Curry discover the default credentials and IDOR flaw during a security review of the McHire platform |
| June 30, 20255:46 PM ET | Researchers contact both Paradox.ai and McDonald’s to report the vulnerabilities under responsible disclosure |
| June 30, 20257:31 PM ET | McDonald’s acknowledges the report; default admin credentials are disabled within less than 2 hours of disclosure |
| July 1, 202510:18 PM ET | Paradox.ai confirms all issues — including the IDOR API vulnerability — are fully resolved |
| July 10–11, 2025 | Wired, SecurityWeek, CSO Online, TechCrunch, Malwarebytes and others publish coverage; global media attention follows |
| July 17, 2025 | Krebs on Security reports additional details: a Paradox.ai developer in Vietnam suffered a separate malware (Nexus Stealer) compromise around the same period |
| Post-July 2025 | Paradox.ai launches a bug bounty programme and commits to further security audits; no evidence of malicious exploitation confirmed |
The speed of the fix is notable — but the McDonald’s data breach had already attracted global media attention within 24 hours of disclosure.
What the McDonald’s Data Breach Exposed: Everything You Need to Know
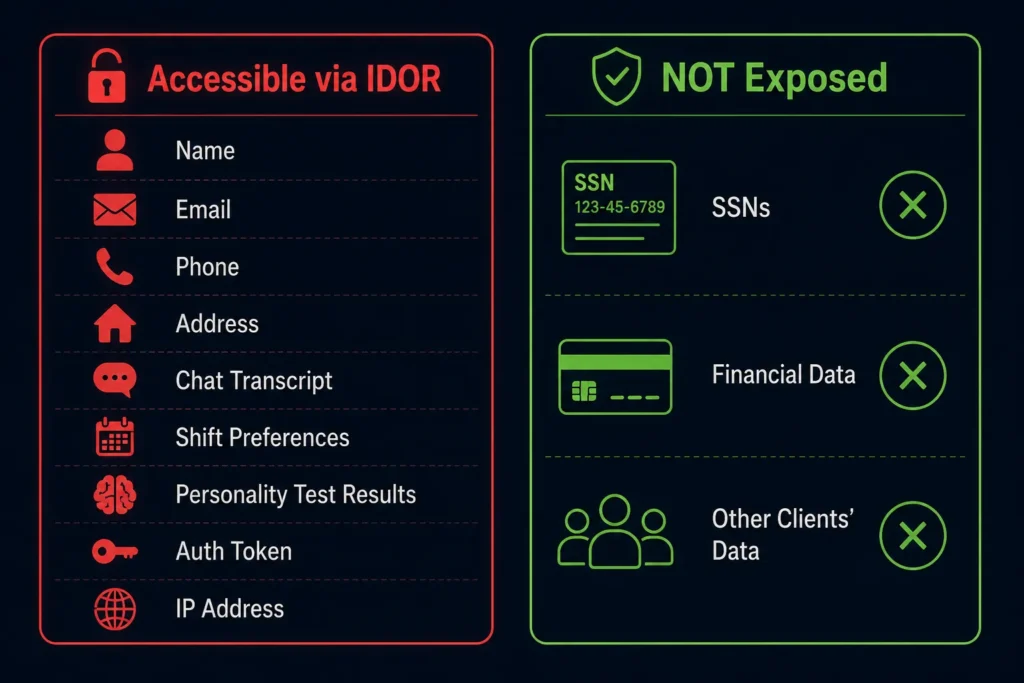
Based on the researchers’ findings, confirmed by SecurityWeek and TechCrunch, the following data types were accessible through the IDOR vulnerability in the McHire platform:
Confirmed Data Types Accessible via the IDOR Flaw
- Full legal name
- Email address
- Phone number
- Home address
- Chat transcripts with the Olivia chatbot
- Shift availability preferences
- Personality test results
- Authentication tokens (which could allow impersonation of applicants on McHire)
- IP addresses
Confirmed NOT Exposed due to McDonald’s Data Breach
- Financial or payment data (not collected by the hiring chatbot)
- Social Security Numbers (Paradox.ai confirmed SSNs were not exposed)
- Data from other Paradox.ai clients (the incident was isolated to McDonald’s McHire instance)
As Malwarebytes noted, even without financial data, this combination is highly valuable to cybercriminals. Full names, email addresses, phone numbers, home addresses, and chatbot transcripts together are sufficient for targeted phishing attacks, social engineering scams, and identity fraud. The authentication tokens were especially dangerous — they could allow an attacker to log into McHire as a specific applicant and potentially manipulate their application.
As security researcher Sam Curry told Wired: “If you wanted to do some sort of payroll scam, this is a good approach.”
What Should You Do Right Now? Urgent Action Steps
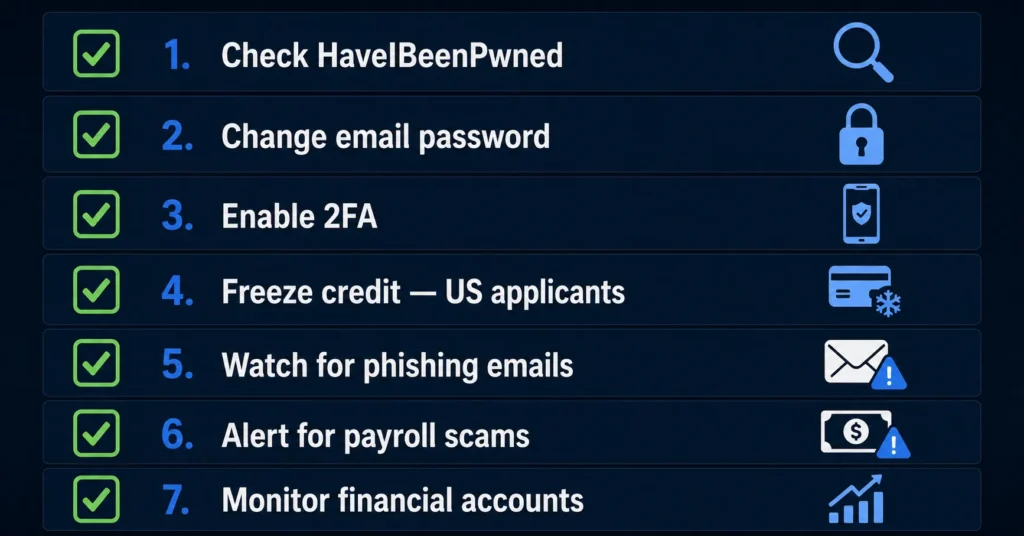
Even though Paradox.ai states the vulnerability has been patched and no data was misused, the risk does not end with the patch. The window of exposure existed. As LastPass’s security analysis notes, opportunistic attackers may have independently discovered the same flaw. Here is what experts recommend:
1. Check HaveIBeenPwned for your email address. Visit HaveIBeenPwned.com and enter the email address you used to apply. Sign up for free breach alerts.
2. Change your password on the email you used to apply. If you reuse that password on other sites — your bank, social media, or any other account — change it everywhere. Use a password manager like Bitwarden or 1Password to generate unique passwords for every site.
3. Enable two-factor authentication (2FA). Turn on 2FA on your email account, financial accounts, and social media. This is your most important defence if credentials are compromised.
4. Freeze your credit (US applicants). The FTC provides a free guide to placing a credit freeze with all three bureaus — Equifax, Experian, and TransUnion. See the FTC’s credit freeze and fraud alert guide for step-by-step instructions. It is free and does not affect your credit score.
5. Watch for McHire or McDonald’s-themed phishing emails. Scammers may use applicant data to send convincing fake follow-up emails or job offer messages. Do not click links or provide additional personal information via email without verifying the sender directly.
6. Be alert to payroll or onboarding scams. As researcher Sam Curry warned, the combination of applicant data and contact information is ideal for fake onboarding or payroll scams. Any unexpected request for bank details tied to a McDonald’s job offer should be verified by calling your local restaurant directly.
7. Monitor your existing financial accounts. Review bank statements and phone bills for unusual activity. Report anything suspicious to your bank immediately.
How to Protect Yourself Going Forward — Practical Security Tips
The McDonald’s McHire incident is a reminder that personal data flows through far more systems than most people realise — including AI hiring tools. Here are practical steps to protect yourself across all future job applications and online activity:
Use a separate email address for job applications. Create a free Gmail or ProtonMail account exclusively for job hunting. If that email is compromised in a breach, your primary email — linked to banking and social media — stays safe.
Never reuse passwords. A password manager (Bitwarden is free; 1Password is excellent) generates and stores a unique password for every site. One breach cannot cascade into others.
Be selective with the data you share in applications. Provide only what is strictly required. If an AI chatbot screening tool asks for your government ID number or full home address before you have even had a human interview, that is worth questioning.
Check HaveIBeenPwned regularly. Set up free monitoring at HaveIBeenPwned.com. It will alert you automatically when your email address appears in a newly reported data breach.
Request data deletion after unsuccessful applications. In many jurisdictions including the EU (GDPR) and UK (UK GDPR), you have a legal right to request that a company delete your personal data. If you applied for a job and were not hired, consider submitting a deletion request.
Expert Analysis: What the McDonald’s Data Breach Means for Cybersecurity in 2026
The McDonald’s McHire incident is not primarily a story about a sophisticated attack. It is a story about elementary security failures at massive scale. A default password that had not been changed since 2019. No multi-factor authentication. An API that did not verify whether a user was authorised to access the record they were requesting. As CSO Online quoted Aditi Gupta of Black Duck: “The rush to deploy new technology must not compromise basic security principles.”
“This incident is a prime example of what happens when organizations deploy technology without an understanding of how it works or how it can be operated by untrusted users. With AI systems handling millions of sensitive data points, organizations must invest in understanding and mitigating pre-emergent threats, or they’ll find themselves playing catch-up, with their customers’ trust on the line.”
— Evan Dornbush, CEO, Desired Effect (via CSO Online)
As Krebs on Security uncovered, the story has an additional layer: around the same period, a Paradox.ai developer in Vietnam suffered a malware infection (Nexus Stealer) that stole credentials for internal Paradox.ai systems including their Okta SSO platform. While Paradox states no data was accessed beyond the researchers’ test, the coincidence of a credential-stealing malware affecting their staff at the same time as this disclosure raises questions about the broader security posture of AI hiring platforms.
For businesses, the lesson is direct: third-party AI tools are your responsibility. McDonald’s did not build McHire, but they deployed it to 90% of their franchisees, and their applicants bore the risk. When you integrate any third-party system — especially one that collects sensitive personal data — you inherit its security posture. Vendor contracts must include security standards, audit rights, and breach notification obligations.
241 days Global average time to identify and contain a data breach in 2025. The global average cost is $4.44 million; the US average reached a record $10.22 million.
Source: IBM Cost of a Data Breach Report 2025 | Analysis: Help Net Security
Conclusion — Stay Informed, Stay Protected
The McDonald’s McHire data breach is a sobering reminder that in our increasingly automated world, personal data doesn’t just flow through banks and hospitals — it passes through chatbots, AI hiring tools, and vendor platforms in ways most applicants never consider. Millions of people handed over their names, addresses, phone numbers, and chatbot conversations simply to apply for a job. The systems entrusted with that data failed the most basic security tests.
The good news: the vulnerability was caught by responsible researchers, patched quickly, and there is no confirmed evidence of malicious exploitation. But the potential scale of 64 million records at risk means this incident will rightly be studied as a defining case study in AI hiring platform security for years to come. The McDonald’s data breach will be studied as a defining case in AI hiring platform security for years to come.
Related: Dangerous AI Threat Intelligence: Why Every Business Needs It in 2026 – understand the AI threat intelligence layer that could have caught the McHire credential flaw before it became a 64-million-record exposure.
The 5 Worst Data Breaches of 2026 — And What AI Could Have Prevented – the McDonald’s McHire incident sits alongside 2025’s most damaging breaches, all sharing one common thread: basic security gaps that AI-powered tools were built to catch.
What Is Claude Mythos AI? The AI That Can Hack Any Software Explained – Understand how Mythos AI from Anthropic is a real threat and how to protect yourself from it.
Frequently Asked Questions
Q1. Was the McDonald’s data breach real, and was any data actually stolen?
Yes, the vulnerability was real and confirmed by both McDonald’s and Paradox.ai. Security researchers Ian Carroll and Sam Curry accessed 7 chat records (5 with personal data) to prove the flaw. Paradox.ai states only the researchers accessed the data and no information was leaked or made publicly available. However, the underlying flaw meant anyone with a McHire account could theoretically have accessed any of the 64 million records in the system.
Q2. What personal data was at risk in the McDonald’s data breach?
The data accessible through the IDOR vulnerability included applicants’ full names, email addresses, phone numbers, home addresses, chat transcripts with the Olivia chatbot, shift availability preferences, personality test results, IP addresses, and authentication tokens. Paradox.ai confirmed that Social Security Numbers and financial data were not exposed.
Q3. What caused the McDonald’s data breach security flaw?
Two vulnerabilities combined: first, an administrator test account with the default username and password ‘123456’ that had been left active since 2019 without multi-factor authentication. Second, an Insecure Direct Object Reference (IDOR) flaw in the platform’s internal API, which allowed anyone with a McHire account to access any other applicant’s records by changing a number in the URL.
Q4. How quickly was the McDonald’s data breach fixed?
Extremely quickly after responsible disclosure. Researchers reported the flaw on June 30, 2025 at 5:46 PM ET. The default credentials were disabled by 7:31 PM ET the same day — less than two hours later. The IDOR API vulnerability was fully resolved by July 1, 2025. Paradox.ai has since launched a bug bounty programme.
Q5. What should I do if I applied for a job at McDonald’s through McHire?
Take these steps: check your email on HaveIBeenPwned.com for breach alerts; change the password on the email address you used to apply; enable two-factor authentication on your important accounts; if you are in the US, consider placing a free credit freeze with Equifax, Experian, and TransUnion; and watch for phishing emails or fake onboarding messages claiming to be from McDonald’s.
Sources
1. SecurityWeek — McDonald’s Chatbot Recruitment Platform Leaked 64 Million Job Applications
2. CSO Online — McDonald’s AI Hiring Tool’s Password ‘123456’ Exposed Data of 64M Applicants
3. TechCrunch — AI Chatbot’s Simple ‘123456’ Password Risked Exposing Personal Data of Millions
4. Krebs on Security — Poor Passwords Tattle on AI Hiring Bot Maker Paradox.ai
5. Dark Reading — Lessons Learned from McDonald’s AI Flub (includes Paradox.ai statement)
6. Malwarebytes — McDonald’s AI Bot Spills Data on Job Applicants
7. AI Magazine — How McDonald’s AI Bot Exposed Millions of People’s Data
8. Hackread — McDonald’s AI Hiring Tool McHire Security Flaw Exposed Candidate Chat Data
9. Adversa AI — McDonald’s AI Hiring Chatbot (Olivia by Paradox.ai) Security Incident
10. CM Alliance — McDonald’s Hiring Bot Blunder: AI, Fries and a Side of Job Seeker Data
11. LastPass Blog — McHack’d: How Weak AI Credentials Served Up a Data Breach12. OWASP — Insecure Direct Object Reference (IDOR) Definition
DISCLAIMER
This article is for educational and informational purposes only. The McHire vulnerability was discovered in June 2025 and patched by July 1, 2025. Paradox.ai states only five applicant records were viewed by the researchers and no data was leaked by any third party. All claims in this article are sourced from the referenced publications above. Breach details may evolve. For full editorial standards, see aisecuritywatch.com/disclaimer.
